Preemptive Cybersecurity in the Age of Agentic Enterprises
Cybersecurity is no longer a tooling problem. It’s an architecture problem, and the architecture is being driven off a cliff by the rise of AI agents.
For decades, security was built around a foundational assumption: humans make decisions, systems execute them. Perimeters were defined. Applications were static. Identities belonged to people. That assumption is now dead and most enterprise security stacks don’t know it yet.
The agentic enterprise changes everything
McKinsey identifies the enterprise shift toward agentic AI as one of the defining technology transitions of this decade. These are not copilots. These are autonomous systems that interpret intent, plan multi-step actions, execute across infrastructure, and learn over time, without waiting for a human to click approve.
That fundamentally changes where risk lives. Risk is no longer at the point of access. It now lives inside autonomous workflows, inside the reasoning chains of agents that act on your behalf, across your systems, at machine speed.
THE CORE SHIFT
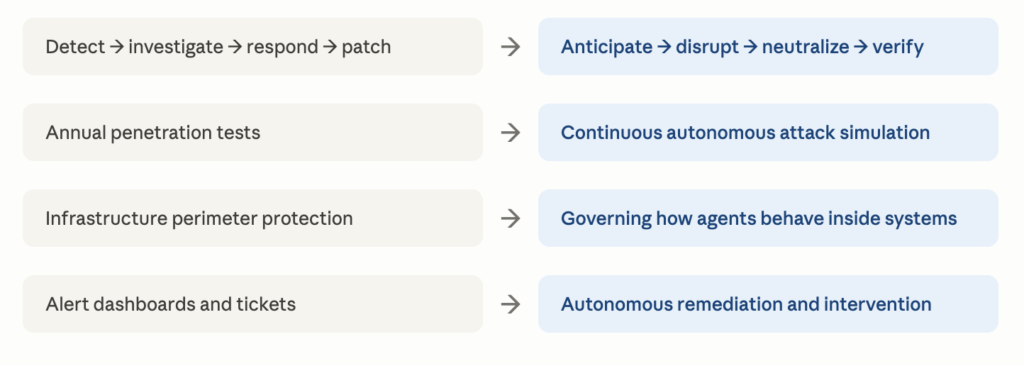
Legacy security was built for static apps, human triggered actions, and clearly defined perimeters. Agentic systems break all three simultaneously, not incrementally. This is not an extension of the old threat model. It is a replacement of it.
Three new attack surfaces legacy tools can’t see
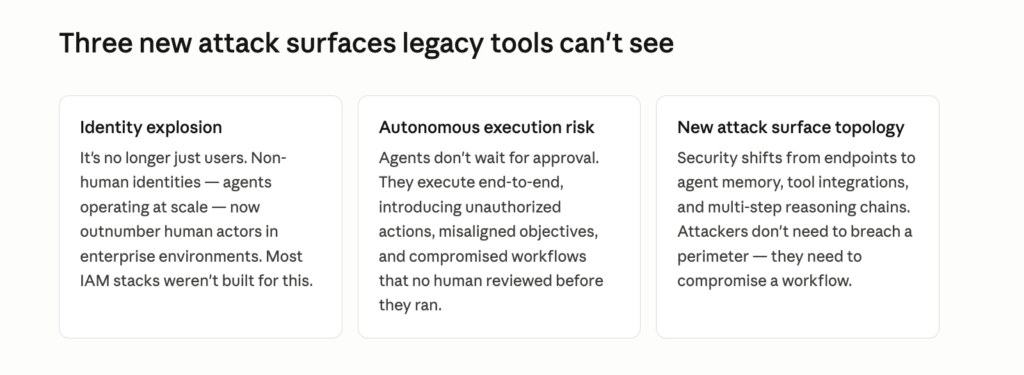
Identity explosion
It’s no longer just users. Non-human identities, service accounts, API keys, automation pipelines, and increasingly, AI agents operating at scale, now outnumber human actors in enterprise environments by a wide margin. In a modern cloud native stack, the ratio can exceed 50:1. Most IAM stacks were designed for a world where identities were attached to people. They weren’t built to govern entities that spin up dynamically, operate without sessions, and can be granted permissions far beyond what any single human employee would ever need. The result is a sprawling, undergoverned identity layer that attackers have learned to exploit systematically, often without ever targeting a human credential at all.
Autonomous execution risk
Human workflows have friction built in. Approval gates, review cycles, and oversight checkpoints slow things down, and that slowness has historically been a security asset. Agents don’t have that friction. They execute end-to-end, often across dozens of connected systems, in seconds. When an agent is misconfigured, manipulated through prompt injection, or operating on a compromised objective, there is no human in the loop to catch it before the damage is done. Unauthorized data exfiltration, misconfigured permissions, deleted records, fraudulent transactions, all of this can occur within a single autonomous workflow before any alert fires. The attack window is no longer measured in hours. It’s measured in API calls.
New attack surface topology
Traditional security was built around a perimeter model: protect the endpoints, monitor the network, control access at the boundary. That model assumed that the most dangerous thing an attacker could do was get inside the wall. Agentic AI has made the wall largely irrelevant. The new attack surface lives in agent memory, tool integrations, multi-step reasoning chains, and the instructions agents receive and act on. Attackers don’t need to breach infrastructure. They need to compromise a workflow, a single poisoned data source, a manipulated tool response, or an injected instruction that redirects an agent’s behaviour entirely. The perimeter has not expanded. It has dissolved, and been replaced by something that looks nothing like what security teams were trained to defend.
The implication is severe: the attack surface has not expanded. It has changed shape entirely.
And AI powered attacks have adapted faster than defenders. In September 2025, Anthropic detected Chinese state sponsored hackers running an intrusion in which AI handled 80–90% of the work autonomously, thousands of requests per second, at speeds no human team could match. Four organizations were breached before detection.
This is not a future threat vector. It is the current operational reality. The question for security leaders is not whether their environment will be targeted through agentic vectors — it is whether their tooling was built for the world that now exists, or the one that existed five years ago. For most enterprises, the honest answer is the latter.
The shift: reactive → preemptive
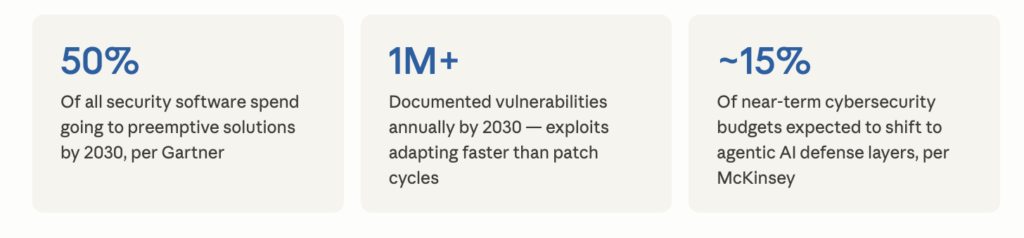
Reactive security cannot keep up with autonomous attacks. The industry has known this for years. What’s changed is that the gap is now binary — either you are running preemptive systems, or you are running behind. Gartner’s 2026 strategic technology report makes this explicit: by 2029, products lacking preemptive cybersecurity capabilities will lose market relevance as proactive defense becomes a universal requirement.
Security for AI is the fastest-growing segment in a $220B market and it’s still Emerging.
McKinsey’s Cyber Market Map 2025 makes the opportunity concrete: across a $220B market, Security for AI sits alone in the Emerging quadrant with the highest forecasted growth rate of any segment — 25%+ annually through 2029.
The paradox: you cannot secure an agentic enterprise without agents
Human-led SOC workflows cannot monitor millions of agent interactions, simulate attacker behavior continuously, or respond in milliseconds. The only credible defense against autonomous attacks is an autonomous defense layer. AI agents become the security control plane.
McKinsey describes this shift precisely: security is moving from infrastructure protection toward governing how humans and agents behave within systems. That creates a new control plane organized around three layers — identity and governance (who or what is acting), entitlement (what they are allowed to do), and verification (how actions are constrained and audited in real time).
Gartner maps the offensive capabilities of this new layer across what it calls the 3 Ds of preemptive cybersecurity:

Sources:
Gartner: Top 10 Strategic Technology Trends for 2026(Preemptive cybersecurity as trend #7, the 3Ds framework, 50% of security spend by 2030) https://www.gartner.com/en/articles/top-technology-trends-2026
McKinsey & Company: Securing the Agentic Enterprise(The $220B market, cybersecurity segment bubble chart, agentic adoption reshaping control planes) https://www.mckinsey.com/capabilities/risk-and-resilience/our-insights/securing-the-agentic-enterprise-opportunities-for-cybersecurity-providers
